Know When Your Vendors Get Hacked — Before It Becomes Your Ransomware Problem.
"Professional-grade early warning for less than the cost of a single hour of incident response."
A Breach That Took a Year to Patch. Don’t Make the Same Mistake.
TSMC didn’t know for over 12 months that MOVEit was compromised. Your vendors won’t tell you either — but SMOKE will.
Read the MOVEit Case Study →iNVISIQ's SMOKE Engine watches those external ‘touch points’ 24/7 and warns you the moment something dangerous shows up tied to your business — so your one IT person isn’t blind.
- You’re not the first target. Cyber criminals break into your vendors, apps, and service providers — then use those weaknesses to reach your business.
- SMOKE spots the attack long before you can. If criminals start probing or exploiting your connected vendors, SMOKE sees the signs instantly.
- When a vendor is breached, SMOKE alerts you immediately so you can block the attack path before the devastation hits your business.
What You Actually Get With SMOKE
No jargon. Just action.
Vendor breach early warning
If a vendor, cloud tool, or service you rely on shows up in breach reports or threat feeds, SMOKE flags it immediately — so you don’t learn about it from the news or after criminals have already moved toward your business.
Monitoring your external attack surface
SMOKE monitors exposed credentials, misconfigured services, and known-exploited vulnerabilities tied to your domains and IPs — then tells your IT person exactly where to focus before attackers do.
Alerts your leadership can understand
Every alert includes a clear, plain-English summary explaining what happened, why it matters to your business, and how urgent it is — so decisions never get stuck in technical jargon.
Step-by-step actions for your IT person
Every alert includes specific, copy-and-paste steps your IT person can execute immediately — not vague recommendations — so issues get handled fast and correctly.
Proof you’re managing cyber risk
SMOKE keeps a record of alerts and the actions taken — giving you documented evidence for insurers, banks, and auditors when they ask, “What have you done about cyber risk?”
Example: If a payroll vendor you use shows up in a ransomware leak, SMOKE sends an alert that includes:
- What happened — in plain English, without jargon.
- What it touches — which vendor, tool, or system in your business is affected.
- What to do in the next 24 hours — concrete steps your IT person must take to cut off the attack path.
Your IT person gets the alert.
You get the alert — because trusting one inbox is how businesses end up in the news.
Want someone else looped in? Add them as CC.
And for extra security, you can enable Telegram — it doesn’t send the alert itself, it simply tells you: “SMOKE just emailed you. Go look.” That’s your anti-phishing, double-check safety line.
And no, you don’t have to log in to some portal you’ll forget the password to. Everything goes straight to email. Period.
1. You map your touch points.
You complete a short onboarding form listing the vendors, tools, and services
your business relies on.
2. We start monitoring.
SMOKE plugs into curated threat feeds and intelligence sources, watching for
anything tied to your domains, vendors, and sector.
3. You get early warning.
When something pops, we send clear, actionable alerts to you and your IT contact
within minutes — before attackers ever get close.
Putting SMOKE in place gives you early warning when your vendors, cloud tools, or connected services are breached — so attackers never reach your business in the first place.
Start Monitoring My Business Contact iNVISIQ DirectlyMonth-to-month · Cancel anytime
Small Business
Typical for 5–50 staff using core cloud tools, a basic website, and a few key vendors.
Medium Business
For growing teams with multiple tools, industry systems, and 20–100 vendors/critical services.
Enterprise / Gov / Edu
For larger organizations, schools, and agencies with complex vendor chains and high exposure.
A touch point is the only piece of jargon we use — and it simply means any system, vendor, tool,
or service your business relies on that could expose you to cyber risk.
Email providers, payroll tools, cloud apps, website hosts, CRMs… they all count as touch points.
And in 2025, most successful breaches start through one of these.
We use touch points to keep pricing fair and your protection accurate based on your real operational size.
* Based on $149/mo plan
❓ Frequently Asked Questions
❓ 1. How can my small business get early warning before cyber threats hit us?
INVISIQ is a behavioral cybersecurity service for small and mid-sized businesses that gives you early warning when cyber threats are forming around your company. It constantly watches the same public sources attackers and ransomware groups watch, then alerts you when something tied to your business or vendors looks dangerous — with clear “do-this-now” actions your IT person can execute.
❓ 2. What’s the difference between INVISIQ and traditional tools like firewalls, antivirus, or SIEM?
Firewalls, antivirus, and SIEM tools mostly watch what is happening inside your own network. INVISIQ behaves like an external radar: it focuses on your internet-facing systems and the vendors, cloud tools, and services you rely on. Instead of flooding you with raw logs, it sends plain-English alerts that explain what happened, why it matters to your business, and what your IT person should do in the next 24 hours.
❓ 3. How can I know when a vendor or third-party service I use has been breached?
Most successful attacks on small businesses now start through a vendor, cloud app, or outside service that was breached first. INVISIQ maps those vendors as touch points and continuously monitors threat feeds, leak reports, and public intelligence for signs they are under attack. When one of your touch points shows up in a breach or active campaign, INVISIQ alerts you so you can block the attack path before it ever reaches your business.
❓ 4. How much does small business cybersecurity monitoring like SMOKE cost each month?
INVISIQ’s SMOKE monitoring starts at a flat monthly price with no contracts. Most small businesses fit into the entry plan, which covers a typical set of vendors and cloud tools, and you can scale up to higher plans as you add more systems and providers. Pricing is based on how many touch points you want monitored — so your cost tracks your real exposure instead of just headcount.
❓ 5. Do cybersecurity monitoring tools track users or fingerprint browsers? What does INVISIQ do?
Many tools collect detailed tracking data, from cookies to browser fingerprinting, to follow users around the internet. INVISIQ does not do that. We don’t use tracking cookies, fingerprinting, or hidden marketing scripts on your site. Our focus is on external cyber threats, vendor exposures, and breach signals — not on profiling you or your staff.

CASE STUDY: MOVEit Breach – A Patch That Took A Year to Land
CASE STUDY: MOVEit – The Patch That Took a Year to Land Or: How “We’ll Get to It” Became the Most Expensive Sentence in The History of Cybersecurity If a billion-dollar global manufacturer can’t outrun a breach from ALMOST TWO YEARS AGO , your two-person IT team isn’t going to Jedi-deflect it either.” –Bradford Allen | iNVISIQ Cybersecurity Behavior Analyst Act I: The Four-Day Head Start On May 27 2023, attackers quietly walked into MOVEit

What to Do in the First 24 Hours After a Software Vendor Gets Hacked
A software vendor gets hacked, and most businesses respond with the urgency of a sleeping cow in a rainstorm. This article lays out what to do in the first 24 hours before another company’s security failure strolls into your business, kicks over the furniture, and hands you the bill.

How to Know If a Vendor Breach Affects Your Business
A vendor breach can become your business problem fast. This article shows how to tell whether a third-party breach affects your data, systems, users, or operations — and what to check before “their problem” lands on your desk.
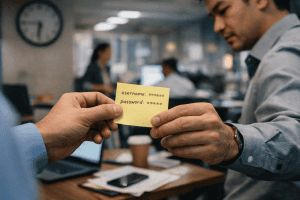
Cybersecurity Isn’t a Technology Problem — It’s an Employee Behavior Problem
🚨 Your Cybersecurity Is Failing Because Anyone With a Phone Can Be a Hacker — and Your Employees Still Work Like It’s 2015 A Behavioral Science Wake-Up Call for Business Leaders in the AI Era Synopsis: Cybersecurity has entered a new era. AI has collapsed the skill barrier for attackers, while employee behavior — especially in work-from-home and hybrid environments — has barely changed. This article breaks down five employee behaviors that now decide whether

2026 Marketing Advice Is Creating Cybersecurity Liability — and Business Leaders Are Letting It Happen
🚨 2026 Marketing Advice Is Creating Cybersecurity Liability And Business Leaders Are Letting It Happen Synopsis Marketing advice for 2026 is accelerating toward AI, personalization, social trust, and automation. This article explains why those same strategies quietly introduce cybersecurity risk — not because the ideas are bad, but because they ignore how people actually behave under pressure. Estimated read time: 9 minutes Word count: ~1,650 words 🧠 Let’s Start With the Uncomfortable Part Most

Redditor – “I Just Want Unrestricted Internet at Work” — And That’s How Businesses Get Breached
A real-world look at modern employee behavior, collapsed boundaries, and why being “not very strict” about internet access is now a business liability in 2026. Synopsis This is not a thought experiment. This is not a fringe opinion. This is not “one bad employee.” This is a real snapshot of how modern employees think about access, privacy, and corporate networks in 2026 — and why that mindset is quietly becoming one of the most dangerous

